Blockchain Evidence Reports & Investigation Documentation
Structured crypto tracing reports built from verified transaction data and documented analysis. No assumptions. No guarantees.
What Our Evidence Reports Provide
Every investigation produces documented findings. These reports organize blockchain data into structured, reviewable format. Therefore, exchanges and compliance teams can assess facts more easily.
Each report focuses on verifiable elements. Interpretations are labeled clearly. Unknowns remain marked as unknowns.
Reports are designed for:
Standard Report Components
Although cases vary, most reports include these sections. However, not every case supports every section. When data is unavailable, that gap is documented.
- Case reference ID
- Transaction verification table
- Wallet interaction map
- Fund flow diagram
- Timeline summary
- Risk indicator review
- Exposure notes
- Traceability limits statement
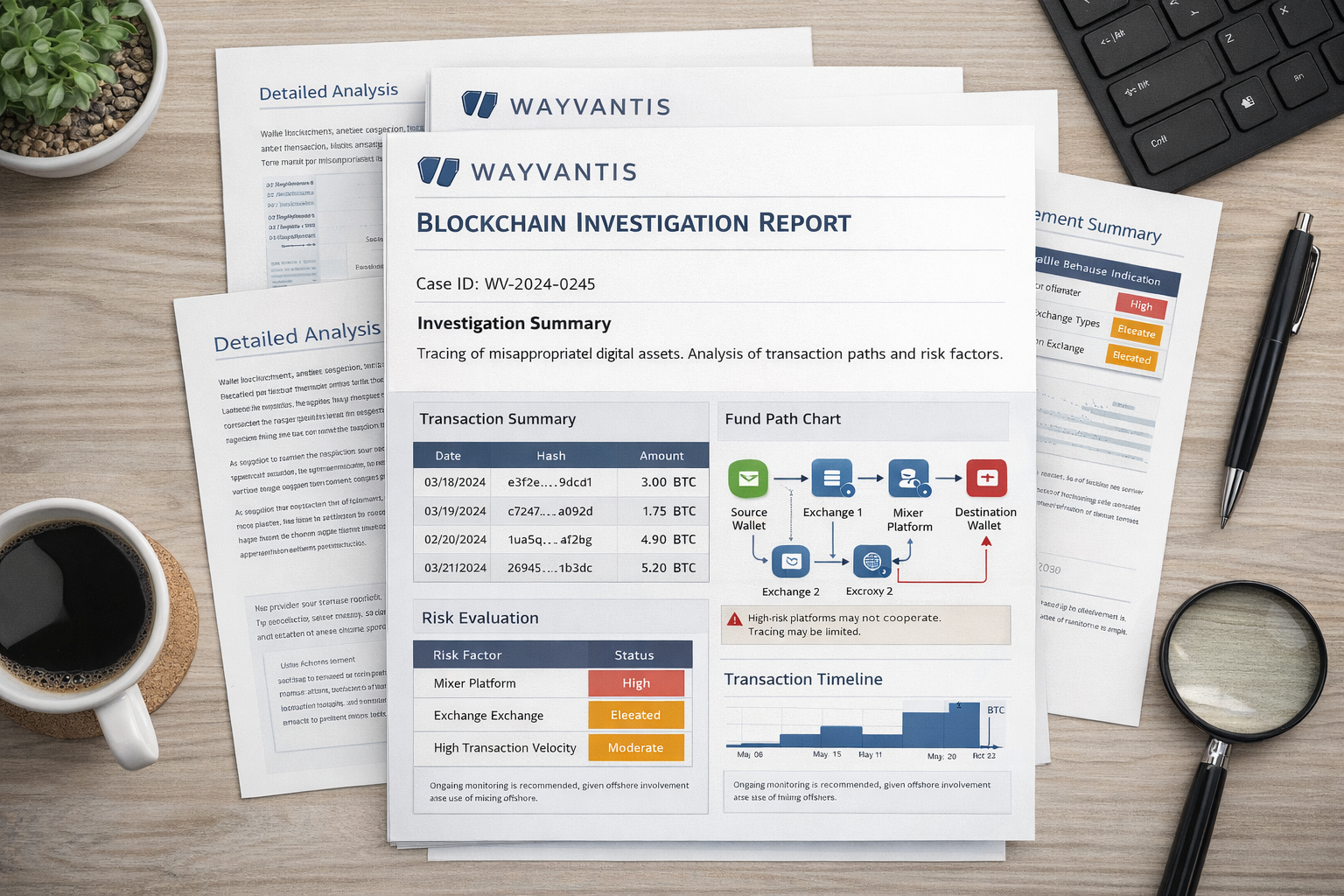

Transaction Flow Visualization
Blockchain movement can be complex. Therefore, reports include visual flow diagrams. These diagrams show asset movement between wallets and platforms step by step.
Visual mapping improves reviewer understanding. It also reduces misinterpretation risk.
Diagram elements may include:
- Source wallet
- Intermediate wallets
- Exchange interaction points
- Aggregation nodes
- Destination exposure points
Visuals support clarity — not conclusions.
Documentation Standards We Follow
Consistency builds credibility. Therefore, every report follows documentation standards.
Source-Verified Data
All transaction data includes source-linked verification and chain-verified hashes.
Structured Format
Reports use consistent tables, sections, and formatting for easy review.
Neutral Language
Descriptions remain factual. Speculative claims are excluded entirely.
Explicit Limitations
Trace boundaries and data gaps are documented clearly, not hidden.
If a conclusion cannot be supported, it is not written.
That discipline protects report integrity.
Traceability Limits Are Always Stated
Blockchain tracing has boundaries. Privacy tools and off-chain transfers reduce visibility. Therefore, reports include trace limits when encountered.
- Mixer obfuscation
- Privacy chains (Monero, Zcash)
- Off-chain settlements
- Non-cooperative platforms
- Incomplete client records
- Cross-chain bridges with low visibility
Limits are documented — not hidden.
Transparency improves reviewer trust.
How Clients Use These Reports
Reports are practical tools, not marketing documents. Clients use them in structured escalation.
Exchange Submissions
Formal case filing with compliance teams using structured evidence.
Legal Consultation
Supporting documentation for legal counsel review and strategy.
Insurance Claims
Documentation for insurance providers requiring evidence of loss.
Fraud Reports
Structured reporting to authorities with clear transaction mapping.
Internal Audit
Record-keeping for organizational compliance and due diligence.
Risk Assessment
Understanding exposure patterns and improving future security.
We prepare documentation. Clients submit through official channels.
We do not claim platform authority.
1. CASE SUMMARY ├── Case Reference: [CASE-YYYY-MM-XXXX] ├── Report Date & Version ├── Executive Summary └── Key Findings Overview 2. TRANSACTION VERIFICATION ├── Source Transaction Analysis ├── Chain Verification Hashes ├── Timestamp Validation └── Address Verification 3. WALLET MAPPING ├── Source Wallet Identification ├── Intermediate Wallet Analysis ├── Cluster Relationship Mapping └── Entity Connection Assessment 4. FLOW DIAGRAM ├── Visual Transaction Path ├── Step-by-Step Movement ├── Exchange Interaction Points └── Final Destination Mapping 5. RISK INDICATORS ├── Address Risk Scoring ├── Behavior Pattern Analysis ├── Mixer/Privacy Tool Detection └── Exchange Deposit Risk Assessment 6. TIMELINE ANALYSIS ├── Chronological Event Sequence ├── Transaction Timing Patterns ├── Speed & Method Analysis └── Correlation with Other Events 7. TRACE LIMITS ├── Privacy Tool Boundaries ├── Data Availability Gaps ├── Visibility Constraints └── Assumptions & Unknowns 8. EVIDENCE APPENDIX ├── Full Transaction Logs ├── Address Reference Table ├── Supporting Documentation └── Methodology Notes
No Fabrication — No Authority Claims
Reports never include unsupported claims or false representations.
- Invented platform contacts or relationships
- Fake freeze notices or legal orders
- Authority impersonation (law enforcement, government)
- Recovery guarantees or outcome promises
- Unsupported attribution or identification
- Exaggerated success rates or capabilities
Only verifiable findings are documented.
Trust grows when restraint is visible.
Not Sure If Your Case Supports a Full Report?
Start with a feasibility assessment first. That step confirms whether investigation depth is meaningful before deeper work begins.
Evidence Report FAQs
Clear answers about our reporting process, limitations, and practical use.
Our report formats are structured for exchange compliance review. However, acceptance depends entirely on individual platform policy, jurisdiction, and specific case details. We prepare documentation to exchange requirements, but cannot guarantee acceptance.
No. Reports document investigation findings only. Recovery depends on exchange cooperation, legal jurisdiction, and case-specific factors. We provide evidence, not outcomes.
Reports identify wallet behavior, transaction patterns, and exposure paths. Personal identification requires exchange KYC data or law enforcement involvement, which we cannot access.
Timeline depends on case complexity. Simple cases: 3-7 business days. Complex cross-chain cases: 2-4 weeks. We provide estimates after initial assessment.
No. Findings remain unchanged. We document verifiable data only. Report integrity depends on factual accuracy, not desired outcomes.
Trace limits are documented clearly in the report. We identify where visibility ends and explain why. This transparency helps avoid false expectations.
Begin With Verified Facts
If you need structured blockchain documentation, start with case assessment first. That step confirms feasibility before deeper investigation begins.
Submit Case Details